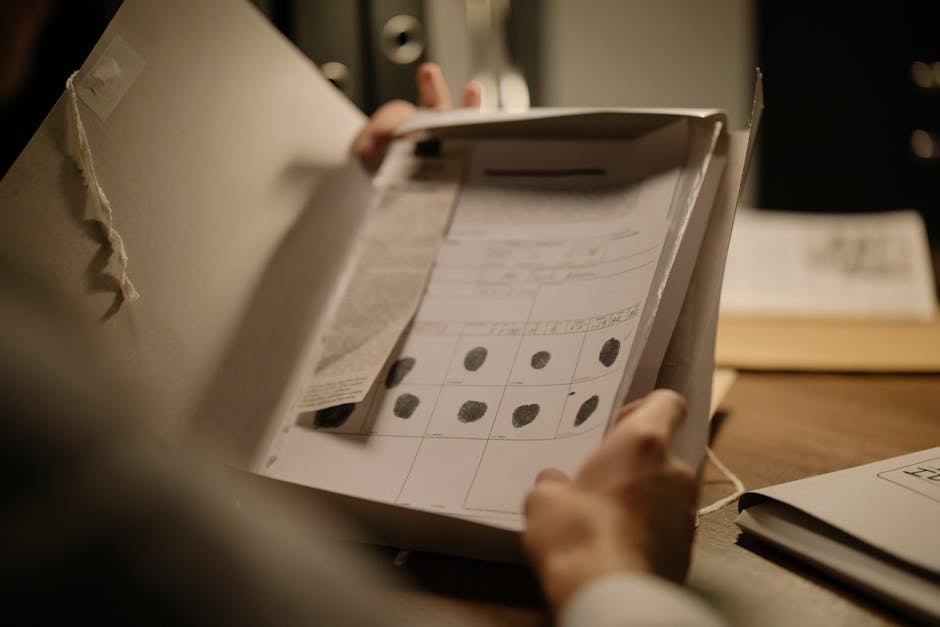
When you open a high-resolution Photoshop (PSD) template for a passport or a utility bill, what you see on the canvas—the intricate guilloche patterns, the crisp typography, and the layered security elements—is only half the story. Beneath those pixels lies a complex architectural layer known as metadata. Metadata functions as a digital fingerprint that chronicles every technical modification and software interaction a document file has undergone since its creation. For professionals in film production, game development, or cybersecurity testing, understanding this hidden data is not just a matter of technical curiosity; it is a critical component of digital forensics and asset management.
Most casual users think of metadata as a simple ‘Date Created’ stamp, but in the context of professional-grade document templates, it is far more expansive. It includes everything from the specific version of the software used to the names of the individual layers and the unique identifiers of the hardware that exported the file. A comprehensive metadata profile can reveal the entire lineage of a document, including the software environment and the specific design iterations it passed through. In this deep dive, we will peel back the layers of document templates to understand what this hidden data reveals and why it matters for legitimate professional use cases.

The Anatomy of PSD Metadata: EXIF, IPTC, and XMP
To understand what a file is hiding, we must first categorize the types of data it stores. In a standard PSD template used for film props or educational simulations, the data is usually organized into three primary standards: EXIF, IPTC, and XMP. The Extensible Metadata Platform (XMP) is the most significant for PSD files, as it allows for the storage of complex, user-defined properties and revision histories. While EXIF (Exchangeable Image File Format) is more common in photography for storing camera settings, XMP is where the ‘ghost’ of the designer lives, tracking the evolution of the document through various edits.
When a template is created, the XMP block begins to fill with “Instance IDs” and “Document IDs.” These are unique alphanumeric strings that do not change even if the file name is altered. Unique identifiers within a file’s XMP block allow forensic tools to link a modified document back to its original source template regardless of subsequent edits. This is how high-end production houses keep track of their assets across multiple departments. If a prop master in London modifies a file created by a designer in Los Angeles, the metadata maintains a persistent link between the two versions, ensuring the visual continuity of the film’s universe.
Then there is the IPTC data, which is often used for administrative purposes. In professional settings, this might include copyright notices, usage terms, or specific keywords. Professional document templates often include IPTC fields that specify the legal licensing and intended use cases to prevent the accidental misuse of the asset in non-authorized contexts. For an educator using these templates to teach students about document security, these fields provide an essential layer of context that clarifies the file’s purpose as a training tool rather than a genuine identity document.
Software Fingerprinting and Versioning Traps
One of the most revealing aspects of metadata is ‘software fingerprinting.’ Every time a file is saved in Photoshop, the software leaves a signature. This isn’t just “Adobe Photoshop 2023”; it’s much more specific. Hidden headers within a PSD file record the specific build number of the software and the operating system version used during the final save operation. If you are using a template for KYC (Know Your Customer) system testing, this is a vital detail. An automated system might flag a file if its metadata suggests it was created on a version of Windows that didn’t exist when the ‘document’ was supposedly issued.
This technical granularity extends to the ‘History’ log. Unless explicitly cleared, Photoshop can store a history of the tools used on the file. The metadata history log can inadvertently store a chronological list of every filter applied and every layer visibility toggle switched during the template’s construction. For a game developer creating realistic world-building assets, this history can be a goldmine for understanding how to replicate certain visual effects across different props. However, for those concerned with privacy or file size, this ‘ghost’ history can be a liability that adds unnecessary bulk to the file.
Furthermore, metadata tracks the fonts used—even those that have been rasterized or removed. If a template once used a specific proprietary font that was later swapped for a free alternative, a trace of that original font might still reside in the file’s internal XML. Internal font metadata can reveal the presence of typographic assets that are no longer visible on the canvas but remain indexed in the file’s resource block. This is why professional design bureaus like John Wick Templates focus on 1:1 recreation of security elements such as guilloche grids, holograms, and microprinting while ensuring the underlying file structure remains clean and optimized for its intended professional application.

Why KYC Systems and AI Are Obsessed with Metadata
In the world of FinTech and security testing, metadata is the first line of defense. Automated verification systems do not just ‘look’ at the image; they ‘read’ the file’s binary structure. Modern AI-driven verification systems use metadata analysis to detect ‘template signatures’ by comparing the file’s internal structure against known patterns of common editing software. If a user submits a ‘photo’ of a utility bill for address verification, but the metadata says it was exported from a design suite five minutes ago, the system will trigger an immediate red flag.
This is particularly important for developers who are building and training these very systems. To build a robust KYC AI, you need both ‘clean’ and ‘dirty’ data. Developers use high-fidelity document templates to generate diverse datasets that help train machine learning models to distinguish between authentic physical captures and digitally rendered documents. By manipulating the metadata of a template—changing the color profiles, the software signatures, or the timestamps—testers can see exactly which parameters trigger their system’s fraud detection algorithms.
There is also the issue of ‘Consistency Checking.’ An authentic document captured by a smartphone will have a very specific set of metadata: focal length, GPS coordinates (sometimes), and mobile OS signatures. A major red flag in document verification occurs when a file lacks the expected sensor noise and camera metadata typical of a physical photograph taken in real-world conditions. When using templates for legitimate testing, professionals often have to ‘re-inject’ realistic metadata or physically print and re-photograph the template to ensure the test case accurately simulates a real-world user submission.
The Hidden Impact of Color Profiles and Layers
Metadata isn’t just about text and timestamps; it’s also about how color is interpreted. Every professional PSD template includes an ICC (International Color Consortium) profile. The embedded color profile in a document template determines how hues are rendered across different monitors and print environments, ensuring visual consistency in film and game production. If a film prop is designed using an sRGB profile but the production’s color pipeline uses ACES, the metadata helps the technical director bridge that gap without losing the ‘authentic’ look of the document.
Beyond color, the way layers are named and organized in the metadata tells a story. In a high-quality template, layers are often named with technical precision—labels like ‘UV Ghost Layer’ or ‘OVI (Optically Variable Ink) Shift.’ The naming conventions used within a template’s layer metadata provide a roadmap for the complex security features that the designer has painstakingly recreated. For a student of graphic design, studying these layer structures is like looking at the blueprints of a high-security facility. It reveals how multiple ‘weak’ effects (like subtle gradients and thin lines) combine to create a ‘strong’ security feature that is difficult to replicate.
Interestingly, some metadata is ‘recursive.’ If you place a Smart Object inside a PSD, that object can have its own independent metadata nested within the parent file. Nested metadata within Smart Objects can preserve the original source data of a component even after it has been scaled, rotated, or filtered within the main document. This can lead to a ‘metadata bloat’ where a seemingly simple 50MB file actually contains 100MB of hidden historical data, potentially slowing down rendering engines in real-time game environments.
The Ethics and Logistics of Metadata ‘Scrubbing’
For many professionals, the goal is to remove as much metadata as possible to protect privacy or to make a prop appear ‘neutral.’ This process, known as scrubbing, is more difficult than it sounds. Simply changing a file format from PSD to JPG does not automatically strip all metadata, as many formats are designed to carry over XMP and IPTC blocks during conversion. To truly sanitize a file, one must use specialized tools that overwrite the binary headers of the document.
In the film industry, this is crucial for ‘clearance.’ Legal departments must ensure that no accidental metadata (like the name of a real-world designer or a private company’s server path) remains in a prop that might be seen in high definition. Production legal teams often require a complete metadata audit of digital props to ensure that no proprietary or third-party information is embedded within the final screen-used assets. This ensures that the fictional world remains separate from the real-world production environment.
However, in educational and testing environments, the goal is often the opposite. Educators may intentionally leave ‘metadata breadcrumbs’ for students to find. In cybersecurity training, instructors use document templates with ‘malicious’ or ‘incriminating’ metadata signatures to teach students how to perform digital forensic investigations and trace file origins. It becomes a game of cat and mouse where the metadata is the primary evidence used to solve a digital puzzle.
Best Practices for Managing Template Data
If you are working with editable document templates for legitimate purposes, there are several best practices you should follow to manage your metadata effectively. First, always work on a copy of the original file. Maintaining a master version of a template with its original metadata intact allows you to verify the asset’s authenticity and technical specifications at any point in the workflow. This is vital for long-term projects like game development where assets may be revisited years later.
Secondly, be mindful of your ‘Export’ settings. In Photoshop, using ‘Save As’ generally preserves more metadata than ‘Export for Web.’ The ‘Export for Web’ function in modern design software provides granular control over which metadata categories are retained, allowing for a balance between file size and data preservation. For web-based simulators or game UI, stripping everything except the color profile is usually the best approach to keep performance high.
Thirdly, use a dedicated metadata viewer. Don’t rely on your operating system’s ‘Properties’ window, which only shows a fraction of the data. Using a dedicated EXIF/XMP viewer allows professionals to inspect the raw XML data of a document template and identify hidden tags that could impact its use in security testing. This level of scrutiny ensures that your ‘legitimate’ file doesn’t have any ‘illegitimate’ signatures hiding in the background.
The Future of Metadata: Blockchain and AI Watermarking
The landscape of document metadata is shifting. We are moving toward a world of ‘Active Metadata,’ where the file itself might report its usage or verify its own authenticity. Emerging technologies like the Content Authenticity Initiative (CAI) are developing secure metadata standards that allow creators to cryptographically sign their digital assets to prove provenance. This will have a massive impact on the document template industry, making it easier to distinguish between high-quality, authorized assets and low-quality, potentially harmful ‘fakes.’
Artificial Intelligence is also being used to create ‘Synthetic Metadata.’ Instead of just stripping data, AI can generate a perfectly plausible, yet entirely fictional, history for a file. Synthetic metadata generation allows for the creation of digital props that possess a realistic but entirely fabricated forensic history, perfect for high-immersion role-playing games or film sets. This adds another layer of realism to the digital assets we use in our media and training programs.
As these technologies evolve, the importance of starting with a high-quality base becomes even more apparent. Whether you are building a simulation, training an AI, or designing a prop for the next blockbuster, the integrity of your starting material is paramount. For those who require the highest level of detail, we recommend exploring resources like John Wick Templates for high-fidelity assets that respect the structural nuances of original documents. By understanding the hidden data within these files, you can use them more effectively, safely, and creatively in your professional endeavors.
Frequently Asked Questions
Does opening a PSD template automatically change its metadata?
Opening a file usually doesn’t change much, but the moment you hit ‘Save,’ the software will update the ‘Date Modified’ and likely add its own software signature to the XMP block. If you want to keep the metadata pristine, it is best to view the file in a ‘read-only’ mode or use a metadata viewer rather than an editor.
Can I manually edit the metadata of a document template?
Yes, there are several tools, such as ExifTool, that allow you to manually write or overwrite metadata tags. This is often done by professionals to ‘re-inject’ realistic data into a file after it has been edited, though it requires a good understanding of the expected data structures for the document type.
Is metadata the same as a digital watermark?
No. A digital watermark is usually a visible or invisible change to the actual pixels of the image, whereas metadata is data stored in a separate section of the file’s code. Metadata is easier to strip than a robust digital watermark, which is why the two are often used together for copyright protection.
Why is my PSD template so much larger than the exported JPG?
This is often due to ‘metadata bloat’ and the storage of layer data. A PSD stores every layer, its history, and potentially nested Smart Object data, all of which have their own metadata. A JPG is a ‘flat’ format that discards most of this architectural data to save space.
Can metadata tell if a document template was used for a specific purpose?
Not directly, but it can provide clues. For example, if a file’s metadata shows it was edited 50 times in a single hour using ‘Forensic Analysis’ tools, it suggests a high-intensity testing environment. Metadata tells you the *technical* history, not the *intent* of the user.

Leave a Reply